Eenvoudige, betaalbare en krachtige cyberbeveiliging voor uw groeiende bedrijf
Cyberbedreigingen zijn al ingewikkeld genoeg. Het laatste waar een bedrijf op zit te wachten, is dus cyberbeveiliging die ook ingewikkeld is. Onze gebruiksvriendelijke zakelijke antivirusoplossingen bieden krachtige bescherming tegen een groot aantal cyberdreigingen, zodat u zich met een gerust hart op uw bedrijf kunt richten.


Approved Business Security Product Award

Approved Corporate Endpoint Protection

Top Performer
najaar 2025


Approved Business Security Product Award

Approved Corporate Endpoint Protection

Top Performer
najaar 2025

Maak een keuze uit onze cyberbeveiligingsoplossingen om te zien wat het beste bij uw bedrijf past.
Home Office

Betrouwbare beveiliging voor uw thuiskantoor
Small Business

Krachtige beveiliging voor kleine bedrijven
Channel Partner

Betaalde beveiliging voor klanten met minder overheadkosten
Functievergelijking
Van eindpuntbescherming en antivirussoftware voor servers tot USB-bescherming en patchbeheer, de bescherming van uw bedrijf bestaat uit vele elementen. Vergelijk onze oplossingen voor kleine bedrijven en kies het beschermingsniveau dat het beste bij uw bedrijf past.
Bedrijven moeten voortdurend controleren op blinde vlekken in de beveiliging om hun apparaten en netwerken veilig te houden. Dit betekent dat effectieve antivirussoftware (in combinatie met best practices) essentieel is in het voorkomen van malware, die kan leiden tot gegevensinbreuken en andere schadelijke activiteiten. Veelvoorkomende aanvallen zijn:
Adware
Trojaanse paarden
Phishing
Spyware
Ransomware
De cyberbeveiligingsoplossingen van Avast Business beschermen u niet alleen tegen deze cyberbedreigingen maar ook tegen botnets, zero-day-aanvallen en SQL-injectie. Lees het artikel Wat is cyberbeveiliging? voor meer informatie over cyberbeveiliging en veelvoorkomende dreigingen.
Wat is het verschil tussen persoonlijke en zakelijke antivirussoftware?
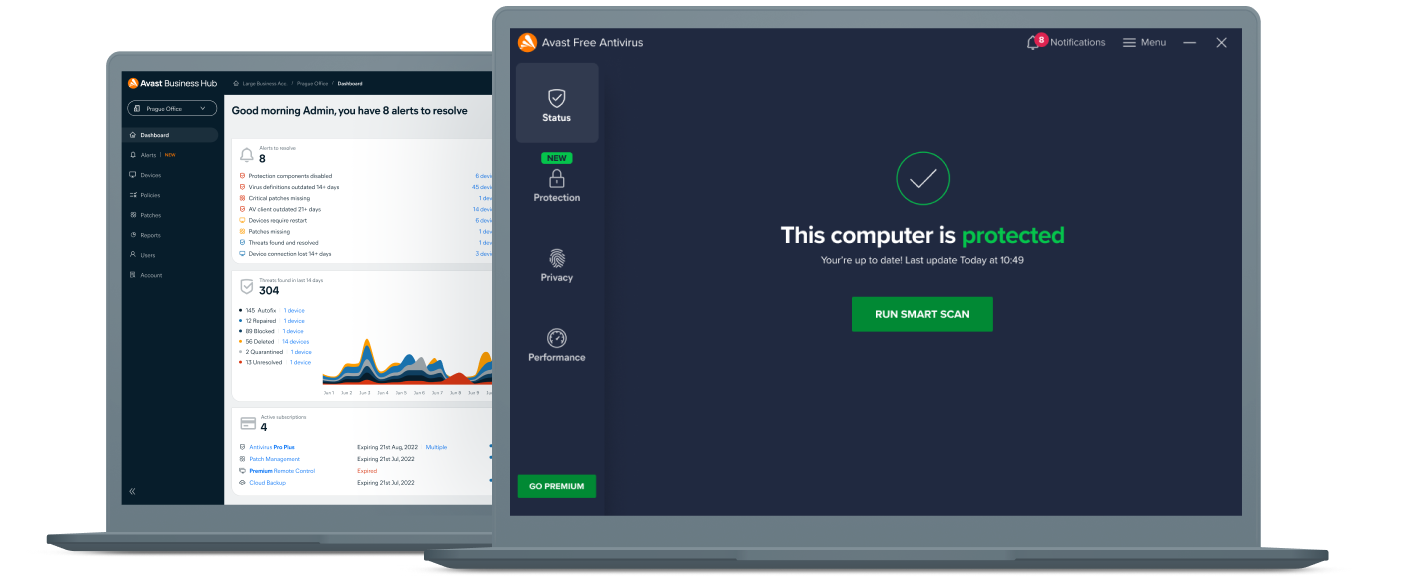
Hoewel beide typen antivirussoftware worden gebruikt om cyberaanvallen te voorkomen, zijn er belangrijke verschillen tussen de software die wordt gebruikt voor persoonlijke antivirus en commerciële antivirus.
Persoonlijke cyberbeveiliging richt zich op het beschermen van individuele apparaten, terwijl zakelijke antivirussoftware het netwerk van een bedrijf moet beschermen, waarin individuele apparaten als eindpunten worden aangeduid.
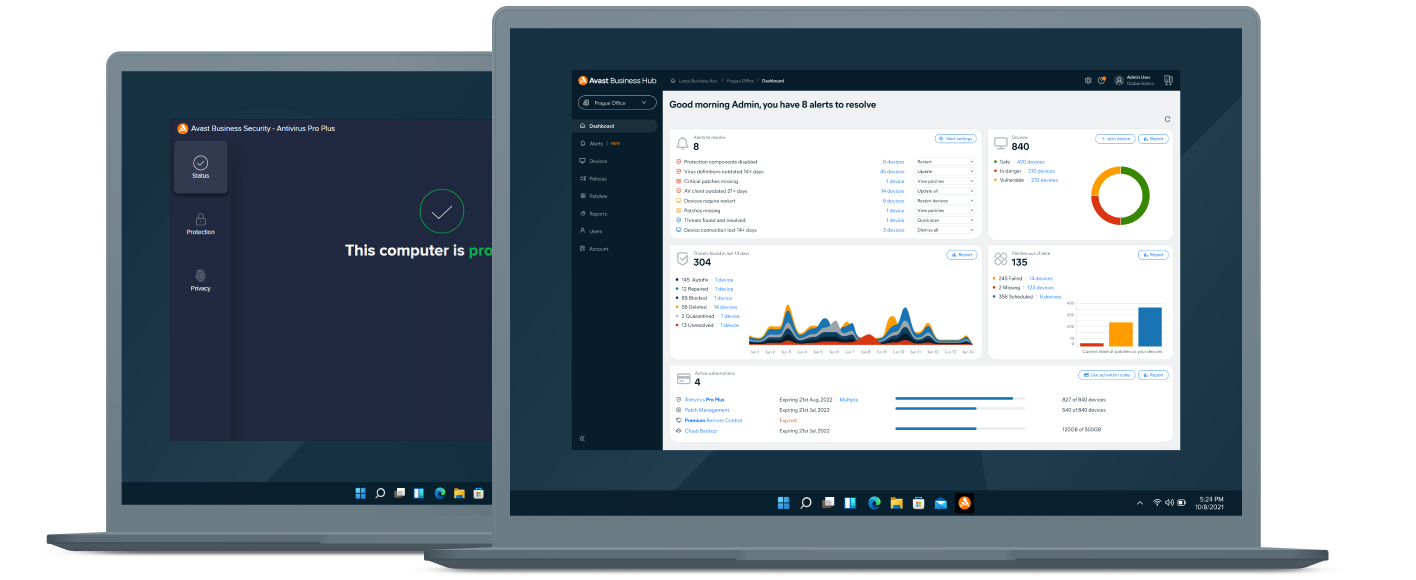
Om op deze manier te kunnen werken, vereist bedrijfsbeveiliging een extra niveau van patchbeheer en hulpprogramma's voor het bewaken en beschermen van meerdere apparaten, evenals cloud- en serverbeveiliging.
Bekijk Avast Free Antivirus voor persoonlijke bescherming.
Geavanceerde cyberbeveiliging gebaseerd op drie decennia aan innovatie
De twee steunpilaren van Avast: cyberbeveiligingstalent en big data. De helft van onze medewerkers houdt zich bezig met onderzoek en ontwikkeling. Daardoor kunnen wij met volle overgave innoveren en beveiligingsoplossingen van wereldklasse ontwikkelen. Onze geavanceerde beveiligingsengine maakt gebruik van gedragsherkenning, zelflerende algoritmen in de cloud en detectie via kenmerken om uw bedrijf betrouwbare bescherming te bieden. Zo houdt u de handen vrij voor belangrijker zaken.
Het resultaat zijn zakelijke antivirusoplossingen en firewallsoftware die uw bedrijf oplossingen voor endpointbescherming en cyberbeveiliging van de volgende generatie bieden.
Wat is de meerwaarde van Avast?
Gebruiksgemak
Bekroond
Betaalbaar
Misschien vraagt u zich nog steeds af...
Veelgestelde vragen
Bezoek ons Ondersteuningscentrum voor meer veelgestelde vragen.

