What is an IP address?
IP address stands for “Internet Protocol address.” The Internet Protocol is a set of rules for communication over the internet, such as sending mail, streaming video, or connecting to a website. An IP address identifies a network or device on the internet.
The internet protocols manage the process of assigning each unique device its own IP address. (Internet protocols do other things as well, such as routing internet traffic.) This way, it’s easy to see which devices on the internet are sending, requesting, and receiving what information.
IP addresses are like telephone numbers, and they serve the same purpose. When you contact someone, your phone number identifies who you are, and it assures the person who answers the phone that you are who you say you are. IP addresses do the exact same thing when you’re online — that’s why every single device that is connected to the internet has an IP address.
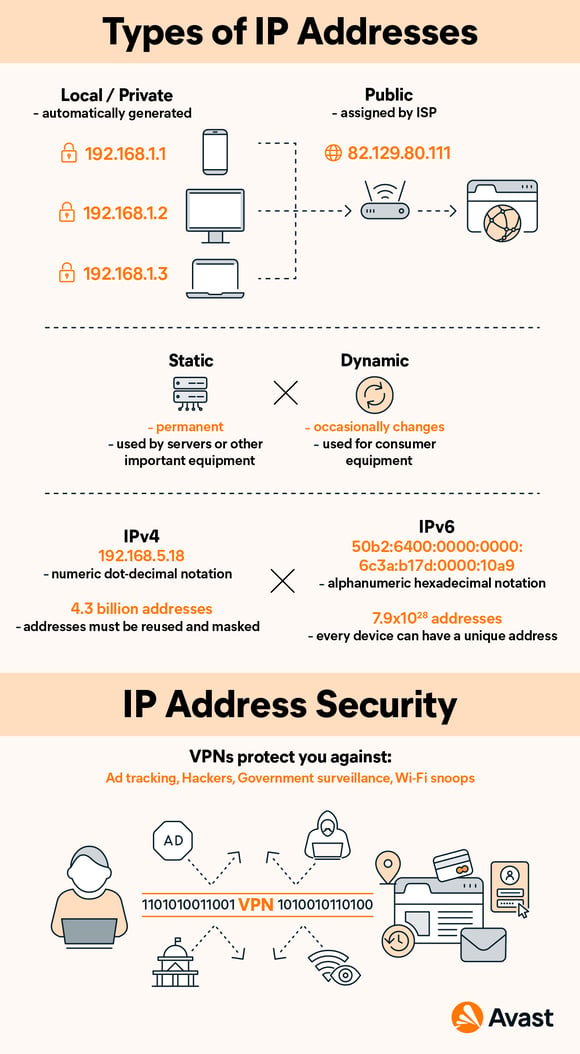
There are two types of IP addresses: IPv4 and IPv6. It’s easy to recognize the difference if you count the numbers. IPv4 addresses contain a series of four numbers, ranging from 0 (except the first one) to 255, each separated from the next by a period — such as 5.62.42.77.
IPv6 addresses are represented as eight groups of four hexadecimal digits, with the groups separated by colons. A typical IPv6 address might look like this: 2620:0aba2:0d01:2042:0100:8c4d:d370:72b4.
You can easily find your IP address. In fact, we have a cheat sheet that shows how to find your IP address on Mac or Windows.
The parts of your IP address
An IP address has two parts: the network ID, comprising the first three numbers of the address, and a host ID, the fourth number in the address. So on your home network — 192.168.1.1, for example – 192.168.1 is the network ID, and the final number is the host ID.
The Network ID indicates which network the device is on. The Host ID refers to the specific device on that network. (Usually your router is .1, and each subsequent device gets assigned .2, .3, and so on.)
You may not always want the outside world to know exactly which device and network you're using. In this case, it’s possible to mask your IP address from the outside world through a Virtual Private Network (VPN). When you use a VPN, it prevents your network from revealing your address.
Where do IP addresses come from?
IPv4 dates back to the early 1980s, when the internet was a private network for the military. IPv4 has a total pool of 4.3 billion addresses, which sounds like a lot. But with all the computers, smartphones, and tablets that connect to the internet, not to mention IoT devices, we have run out of IPv4 addresses. In fact, we began running out in the 1990s. Very clever technical networking tricks have kept things going.
The Internet Engineering Task Force (IETF), which designs the backbone technologies of the internet, came up with IPv6 about a decade ago. It has a potential pool of 340 undecillion addresses — that’s the number 340 followed by 36 zeroes — meaning we can (in theory) never run out of addresses. It is slowly replacing IPv4, but for now, the two co-exist.
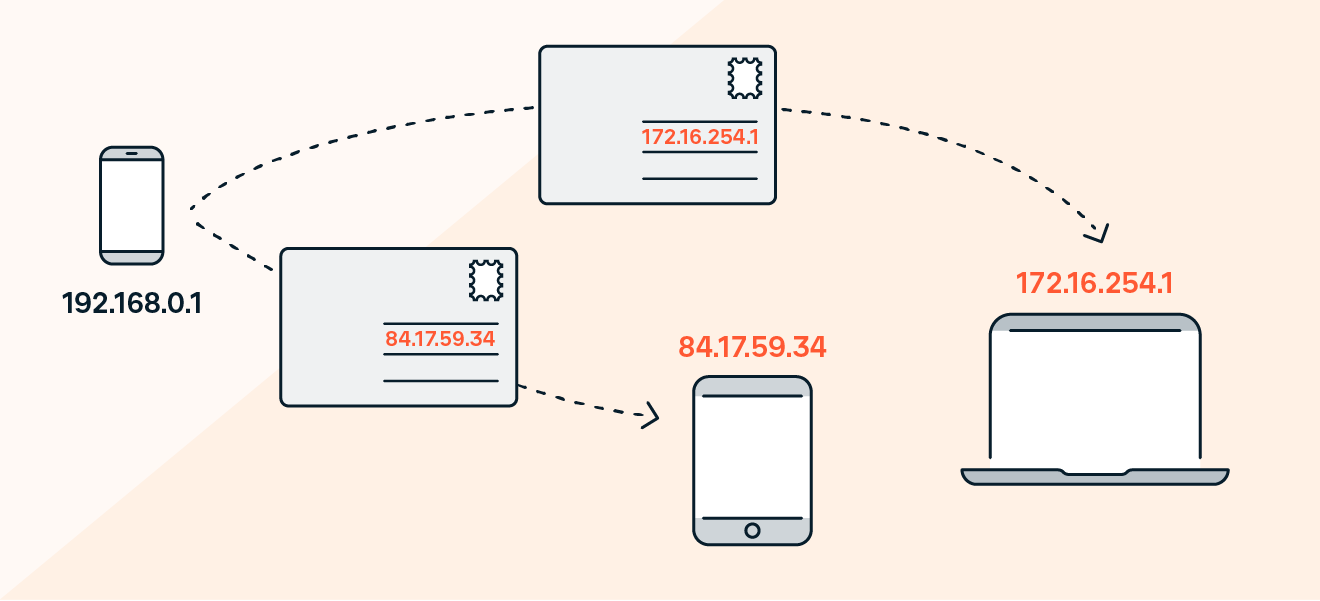
Public vs. local IP addresses
There are two types of IP addresses: external, or public IP addresses; and internal, also called local or private addresses. Your internet service provider (ISP) gives you your external address. When you surf the web, the site you're visiting needs to know who you are (for traffic-monitoring reasons). Your ISP uses your external IP address to introduce you to the website and establish the connection.
You have a different IP address for internal purposes, such as identifying your devices within a home network or inside a business office. The local or internal IP address is assigned to your computer by the router, which is the hardware that connects a local network to the internet. In most cases, that internal IP address is assigned automatically by the router (or cable modem).
Here’s what matters: In most cases, you'll have a different IP address internally than you do on the public internet. Your local IP address represents your device on its network, and your public IP address is the face of your network to the greater internet.
How do IP addresses work?
The post office uses your physical address as a marker for the real-world location of a person, residence, or business. It’s how mail is routed. It’s where you reside. It’s how others know where to find you.
All of these descriptions apply to an IP address, in a digital way. An IP address is where a computer resides, in a virtual sense. IP addresses may identify your own computer, a favorite website, a network server, or even a device (such as a webcam).
IP addresses are especially important for sending and receiving information. They route internet traffic where it needs to go, and they direct emails to your inbox.
The important thing to remember is this: Every active device on the internet has an IP address.
First, TCP/IP...
IP addresses are only one part of the internet’s architecture. After all, having a postal address for your house is meaningless unless there’s a post office responsible for delivering the mail. In internet terms, IP is one part of TCP/IP.
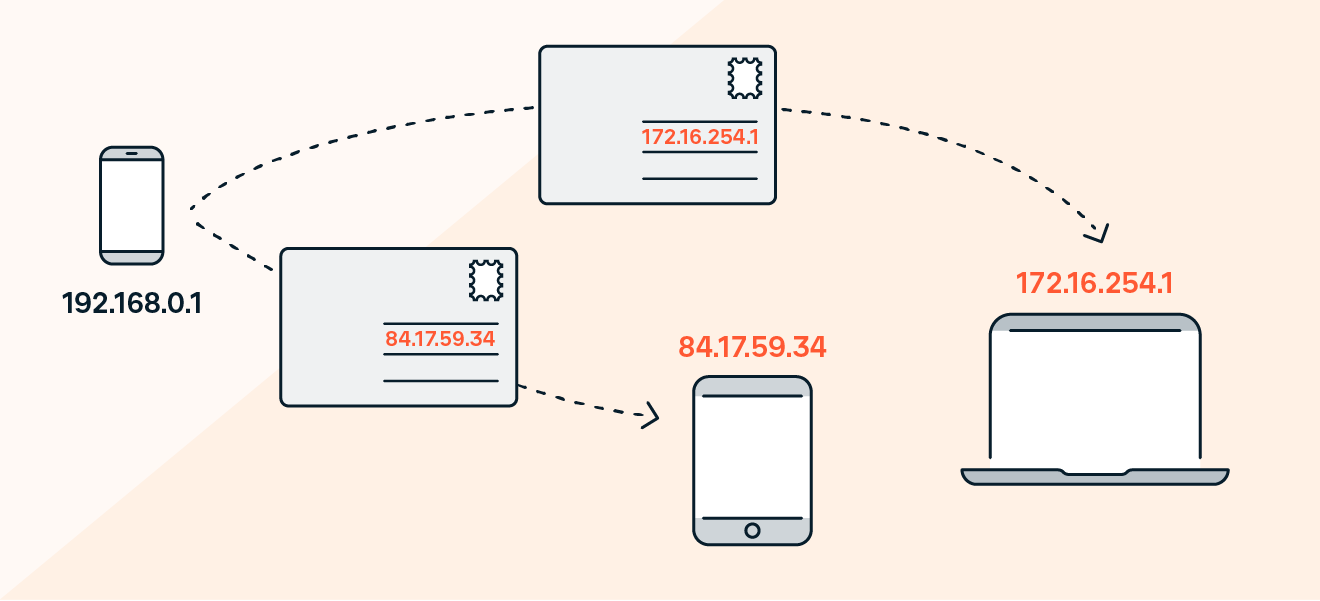
The Transmission Control Protocol/Internet Protocol (TCP/IP) is a set of rules and procedures for connecting devices across the internet. TCP/IP specifies how data is exchanged: Data is broken down into packets and passed along a chain of routers from origin to destination. This is the basis for all internet communication.
TCP defines how applications communicate across the network. It manages how a message is broken down into a series of smaller packets, which are then transmitted over the internet and reassembled in the right order at the destination address.
The IP portion of the protocol directs each packet to the right destination. Each gateway computer on the network checks this IP address to determine where to forward the message.
How IP addresses are assigned: dynamic vs. static
IP addresses can be permanent (static) or temporary (dynamic). The difference between static and dynamic IP addresses is that while the former never change, the latter can and do.
Static addresses are mostly used by businesses, since their websites and web applications must be reliably accessible at all times. But your home IP address doesn’t have to stay the same, since it’s only needed when you’re using the internet.
Your ISP will usually give you a dynamic IP address. While your IP address may not change often, it’s possible to receive a new one from your ISP every time you reboot your computer. The same holds true with the local IP addresses your home wireless router assigns to your laptop, tablet, or smartphone. These devices might get a new address every time you restart your router.
The only real negative with dynamic addresses is that a given computer can’t be reliably found. That makes it difficult to, say, run a web server in your home, as the address might change and no one would be able to find you. Many ISPs allow you to make arrangements for a business connection with a static address if you want to run a server.
A packet's journey
Every time you visit a website, your trip is routed through a complex and hidden series of hops through major traffic backbones. It’s akin to an integrated highway system. A visit to a website might involve a dozen hops, all of which take place near-instantaneously and behind the scenes.
Whether you’re sending an email, loading a webpage or watching a video, all data sent over the internet is broken up into packets. Think of it like a bucket brigade, where buckets of water are passed down a line of people.
Best of all, you usually don’t need to know how it works. One of the coolest things about the internet’s design is that it keeps this structure wholly invisible to ordinary users. This way, you're free to focus on what you need to do, without worrying about how it gets done.
Each packet has a maximum size of 1,500 bytes and includes a wrapper with a header and a footer. The information in the wrapper communicates the type of data in the packet, where it came from, where it’s going, and how it fits together with other packets.
As packets travel, they move in a stream, but all the packets don’t always take the exact same path. If there is congestion across the internet, various packets from the same message might travel across different network backbones. As the packets arrive, the receiving computer reassembles the packets into the original (and final) data.
That’s one reason that IP addresses are so important. Because every packet includes the IP address for its origin and destination, the internet can make sure that all packets reach the right destination.
DNS servers
The Domain Name System (DNS) makes the modern internet possible. The DNS pairs website names you can easily remember with IP addresses that computers can use.
IPv4 addresses are every bit as valid as a website’s alphabetical name. You can type 157.240.22.35 into your web browser, and it’ll take you to Facebook. But who’s going to remember that? Most of us barely remember our own phone numbers.
What the experts say
"When a domain name is entered into a web browser, the computer first checks its local cache to see if it already knows the corresponding IP address. If the IP address is not found locally, the computer queries a DNS resolver."
Familiar domain names are substitutes for real IP addresses. In the early days of the internet, you could connect to another site only by typing in the numbers of its IP address. But thanks to the DNS, we don't need to do this anymore.
The DNS freed us from the headache of remembering IP addresses by giving each site a name. DNS servers sit between your browser and the site you want to visit. When you type a URL into your browser, your browser looks up that domain name in the DNS server, retrieves the corresponding IP address, and sends you to the site you want. All without you, the user, needing to do a thing.
What is the purpose of an IP address?
The purpose of an IP address is to handle the connection between devices that send and receive information across a network. The IP address uniquely identifies every device on the internet; without one, there’s no way to contact them. IP addresses allow computing devices (such as PCs and tablets) to communicate with destinations like websites and streaming services, and they let websites know who is connecting.
An IP address also acts like a return address on postal mail. When a letter you've mailed is delivered to the wrong address, you get the letter back if you include a return address on the envelope.
The same holds true for email. When you write to an invalid recipient (such as someone who left their job and no longer has a company email address) your IP address lets the company’s mail server send you back a bounce message so that you know your email wasn't sent to the right place.
IP addresses and geolocation
In addition to making sure other computers on the internet can communicate with yours, IP addresses also mark the real-world location of your device. This comes in handy when a website wants to customize itself to suit your needs — such as by automatically changing its language, or showing you products that are available in your country. Streaming platforms can also use your IP address to show you the content that they’re allowed to provide you based on where you live.
While your IP address won’t give away your precise location, it can get pretty close. Your IP address can be used to identify your city, postal code, internet service provider (ISP), and latitude and longitude. Since you may not want everyone in the world knowing roughly where you are, consider hiding your IP address with a VPN.
Rather than broadcasting your real IP address to the world, a VPN, like Avast SecureLine VPN, masks your IP address behind another one. This way, anyone else on the internet will only see your VPN’s IP address, while yours remains protected.
How to find your IP address?
Whether you’re using Windows or macOS, you can easily find your IP address within your computer’s network settings. On Windows 10, visit your Network & Internet settings from the Settings menu. If you’re using a Mac, you’ll want to visit the Network section of your System Preferences. Alternatively, simply visit Avast's IP address checker to find your public IP address.
Check out our comprehensive guide to finding your IP address for complete directions on all Windows versions as well as on macOS.
IP address security
You should protect your IP address for all the reasons you would protect your home address. Cybercriminals may attempt to take advantage of you for a variety of reasons. With your IP address, they might be able to:
-
Download or access illegal content: Pirates can download movies, music, and other content and appear to be you, so you could get in trouble with your ISP for something you didn’t do.
-
Trace your home address: It is possible to trace an IP address to a real-world address, exposing you to potential physical danger or robbery when you are not home. Security experts have long advised people to never say on social media that you are on vacation, because that tells criminals you’re not home. It’s a good idea to follow that advice for privacy reasons.
-
Spy on your private internet traffic: Your sensitive personal data, including financial information, can be at risk when hackers are able to access your IP traffic.
-
Directly attack you: In a DDoS (distributed denial-of-service) attack, cybercriminals flood a server with so much traffic that it becomes overwhelmed and shuts down. Consider adding privacy tools to your online toolset, including one that hides your IP address.
Protect your IP address
The Consumer Technology Association recommends that you protect your IP address, such as by using a virtual private network (VPN) to hide it from cybercriminals seeking to commit identity theft or fraud.
Avast SecureLine VPN can protect your IP address from anyone attempting to spy on your IP traffic to capture sensitive financial or personal data. With Avast’s bank-grade encryption, which masks your IP address and sends your communications through a secure tunnel, you’ll enjoy a safe and private internet experience every time you log on.




/Public-vs-local-IP-addresses-Thumb.jpg)