Can ransomware be removed from your Mac?
If you’re one of the unfortunate few that needs to get rid of Mac ransomware and recover encrypted files, we can assure you that both processes are doable, but not always easy. And we’ll level with you: in some cases, file recovery is impossible. As cybercriminals develop more sophisticated ransomware attacks, their targets, be they Mac or Windows users, are having a harder time recovering their files.
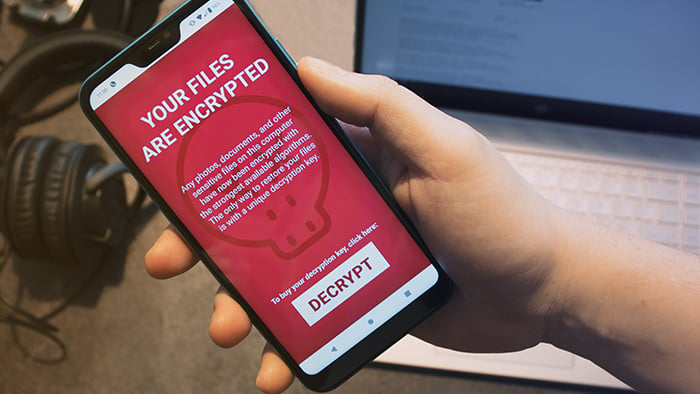
The strain of attack determines the simplicity or difficulty of Mac ransomware removal. You can, for example, do away with the browser-locking FBI / MoneyPak scam in minutes. On the other hand, encryption ransomware can be a nightmare. Also known as filecoders, they bar access to your precious files through encryption. In this case, successful ransomware removal is a minor victory; data decryption is the only way you’ll be able to recover your files. Cybercriminals are banking on your inability to do so, demanding payment for a decryption key that will release your files.
 Image source: https://cdn2.hubspot.net
Image source: https://cdn2.hubspot.net
Each filecoder has a unique encryption method, so removal and recovery aren’t as straightforward as they are when you’re dealing with other types of malware. To help keep ransomware off your Mac and remove it in the unlikely event that a strain slips through, you can turn to Avast One. Even if the encryption remains, you can stop the spread of the ransomware through the private and public networks your Mac is using.
STEP 1: Immediately isolate infected devices
If your Mac is infected with ransomware, immediately find and disconnect all infected wired and wireless computers, tablets, and smartphones on your network, regardless of their operating system. This keeps the malware from spreading to other computers and/or mobile devices.
As you take care of this, make sure you disconnect everything connected to the devices on your network, including:
If you think any of these devices were connected to the infected computer, check their systems for ransomware as well.
STEP 2: Find out which strain of Mac ransomware is on your computer
Once you’ve isolated the infected devices, you’ll need to determine the type of Mac ransomware you’re dealing with. This knowledge could lead to a solution.
The most problematic types of ransomware are filecoders like KeRanger or MacRansom. Other variants, like screenlockers, are generally easier to remove. Here’s a brief overview of the most common types of Mac ransomware:
-
Filecoders encrypt and lock files on your Mac. The cybercriminals behind this type of ransomware demand payment for decryption keys, usually by a deadline, at which point they promise to damage, destroy, or permanently lock your files. Around 90% of ransomware strains are filecoders.
 Image Source: https://167974-484938-raikfcquaxqncofqfm.stackpathdns.com
Image Source: https://167974-484938-raikfcquaxqncofqfm.stackpathdns.com
-
Scareware opens pop-up ads, fake web pages, or a scanning application with fake results, all pushing you to pay for a bogus Mac malware cleaner to remove issues that your computer doesn’t have. As long as you don’t click on the ads, pages, or app, you can get rid of this type of ransomware easily.
 Image Source: https://www.pcrisk.com
Image Source: https://www.pcrisk.com
-
Doxing is the threat of publication of sensitive personal data such as usernames, passwords, email addresses, and credit card numbers. While it isn’t specifically malware, doxing involves a ransom: you receive an email or message telling you that cybercriminals have your private information and, unless you pay a fee, they will make it available on the Dark Web. Our free Avast Hack Check tool can tell you whether any of your passwords have actually leaked or been stolen, while our advanced identity theft checking tool provides comprehensive data protection.
-
Screenlockers do just that: they lock your screen so you can’t access your Mac. The most common variant seen in the wild has been the above-mentioned FBI / MoneyPak scam, which locks your Safari web browser and demands payment to unlock it. Screenlockers are more common on Android devices; nevertheless, you’d be wise to remain vigilant while using Safari.
As a Mac user, you can rest a bit easier than Windows users, but that doesn’t mean your machine is immune. All four threats listed above can infect unsuspecting Mac and iOS device users, too — it just takes one bad click or tap!
Use Crypto Sheriff’s tool to identify the strain of Mac ransomware
To help you determine the type of ransomware on your Mac, we recommend using No More Ransom’s Crypto Sheriff. This handy tool, provided by Europol’s European Cybercrime Center, shows you which of your files have been encrypted and also checks the ransom note. If Crypto Sheriff recognizes the encryption and has a solution, it provides you with a link to download the decryption program you need for your Mac.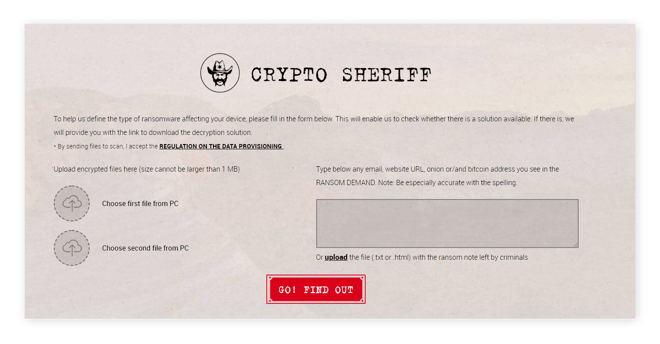
Visit tech forums to learn more about the types of Mac ransomware
You can also visit troubleshooting and tech support forums to find information about the Mac ransomware strain you’re dealing with. Forum members tend to keep discussions up to date, so you might find a thread that offers a fix for new variants, or one in which forum members have joined forces to find a solution.
Some Mac ransomware infections, such as FindZip, create new files with names like "README.txt", "DECRYPT.txt", or "HOW_TO_DECRYPT.txt" and place them on your desktop or bury them in system folders. They may also rename files and file extensions (e.g. .docx or .dll). When you visit tech forums for help, search for these filenames as they can lead you to threads with information about the Mac ransomware you want to remove.
We recommend visiting these forums:
STEP 3: Remove ransomware malware from your Mac
Once you know what you’re dealing with, you can start the Mac ransomware removal process. You have four options:
-
Wait for the ransomware to delete itself (which it often will)
-
Get rid of it with Avast One
-
Have our experts at Avast Premium Tech Support remove it
-
Remove the malware manually
Option A: Check if the ransomware program deleted itself
In many cases, the ransomware on your Mac simply removes itself after encrypting your files. Cybercriminals want their malware to survive in the wild; therefore, they don’t want it leaving behind clues that could crack their strain’s encryption and render it harmless.
Option B: Remove the malware with free Avast Security
Avast One is a free tool that detects and deletes known strains of ransomware programs quickly and easily. It can also help keep your Mac safe from newly released cyberattacks. The free version handles Mac ransomware identification and removal, and it includes an extra layer of defense against future strains of ransomware and keeps your files from being encrypted.
Option C: Let Avast Premium Tech Support remove Mac ransomware for you
Get in touch with our experts at Avast Premium Tech Support (APTS) to have them rid your Mac of ransomware. APTS is a paid service offering 24/7 support for all your hardware and software issues. Our team can help you with ransomware removal, though they are unable to recover encrypted files.
Option D: Remove Mac ransomware manually (ADVANCED MAC USERS ONLY)
In most cases, one of the three options listed above will be all you need to remove ransomware from your Mac. However, ransomware attacks are constantly evolving and growing in number, so there is always the possibility of getting hit with a strain that none of the aforementioned methods can handle. In that case, you might feel your only option is to clean your Mac yourself.
If you decide to take the DIY route, we strongly recommend you start by checking out the above-mentioned online forums. These communities are committed to keeping up with the latest developments in ransomware and finding solutions as quickly as possible, so you’re likely to get solid advice from their members.
STEP 4: Recover your encrypted files
You’ve removed the underlying malware, but that alone won’t recover your files. Here are a few methods that can help you get your files back:
Option A: Restore your system from a backup
You can get your Mac back up and running easily if you’ve been backing up its operating system. Ridding your computer of the malware that’s locking your system or holding your files hostage will stop encryption from spreading through your Mac and network, which means you can still recover your files from a backup.
The backup recovery method is highly effective when you’re dealing with a pesky screenlocker, which doesn’t encrypt your files. Even though you’re more likely to be wrestling with a filecoder that keeps you from accessing your files through — you guessed it — encryption, you can still use your Mac’s Time Machine to roll your system back to its “pre-attack” state and restore encrypted files. So, if you’ve set your Time Machine up to do automatic backups, your files are ready and waiting for you to recover them.
 Image Source: https://support.apple.com
Image Source: https://support.apple.com
Also be sure to take a look inside your iCloud account, as you might have unencrypted backups of personally valuable files like photos and documents created with Apple applications.
As a last resort, you could also use file recovery software like Wondershare Data Recovery for Mac.
 Image Source: http://www.recuvaformac.com
Image Source: http://www.recuvaformac.com
Option B: Use decryption tools
If the ransomware identification methods discussed above have revealed that a filecoder has infected your Mac and encrypted your files, you may be able to use a decryption program to recover your files. If you happen to be a victim of the FindZip strain, you’re in luck: we have a tool to help you take care of the decryption process.
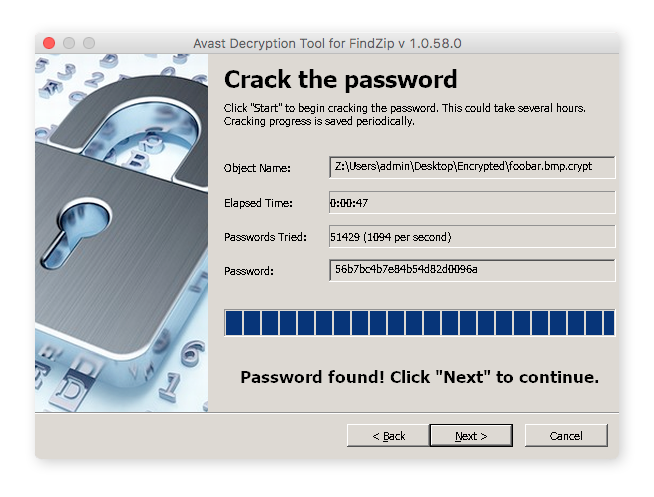
While the majority of our free Avast decryption tools are for Windows PCs rather than Mac computers, you should still take a look at them. In addition to information about known strains of ransomware, filename changes, and ransom notes, they also include a free downloadable decryptor for each variant.
Unfortunately, most types of ransomware haven’t been decrypted, so no programs exist yet that can recover your files. In these cases, you’ll have to either rely on restoring files from a backup or simply wait for the release of a free decryption tool that can handle the ransomware strain on your Mac.
Option C: Don’t pay the ransom and don’t negotiate
If you still can’t recover your files after following all the instructions above, we strongly recommend waiting for a decryption tool for the strain of ransomware on your Mac. Sometimes, the malware exposes lines of code that can lead to a fix.
 If you get hit with ransomware, don’t pay the ransom.
If you get hit with ransomware, don’t pay the ransom.
We understand that you want to get your files back ASAP, but we urge you to never pay the ransom. Just as importantly, don’t attempt to negotiate with your Mac’s attacker. Giving in to their demands will only encourage future ransomware, spurring attackerson to keep hijacking devices and developing new strains. These attackers could also be using their ill-gotten gains to fund other illegal activities.
One last thing: paying the ransom does not guarantee that your attacker will delete the ransomware, unlock your Mac, or give you the decryption tool for their strain. Many hackers want to develop a reputation for keeping their word, in the hopes that future victims will be more willing to pay, but this isn’t always what happens. There have been several cases in which hijackers collect the ransom and then vanish or send decryptors that don’t work. You could even end up paying a completely different ransomware attacker.
Common Questions
These are some of the most frequently asked questions about Mac ransomware.
Can Macs get ransomware?
Let’s get one thing straight: Macs are not immune to ransomware or any other form of malware.
There was a time when Macs may have seemed impenetrable, because cybercriminals focused primarily on attacking Windows machines (which have a far larger, and therefore more lucrative, user base). Apple’s macOS operating system, previously known as OS X, has powerful built-in protection that requires more effort to infiltrate. And yes, Macs cannot be affected by some filecoders like WannaCry, because these strains exploit Windows-specific weaknesses.
Yet, Mac hijackers are continuously developing new malware, and simply having a machine that runs on macOS is no longer enough. While PCs are more prone to hijacking than Macs, Macbooks and iMacs still need Mac security protection: backup provider Datto’s 2018 Ransomware Report states that ransomware attacks on Mac computers grew by 500% in just one year.
How common is Mac ransomware?
The rise of Mac ransomware over the past couple of years is cause for concern — it exists and is likely to continue growing. While it is relatively rare compared to ransomware that targets Windows and mobile operating systems, you should still be vigilant when you’re online and take appropriate measures to keep your Mac safe. Just one ransomware infection could ruin your life. Seriously: imagine losing all your photos, videos, documents, and so on, business and personal. Now, take a few minutes to implement the preventative measures we’ve suggested so that scenario stays in your imagination.
Are Mac browsers vulnerable to ransomware?
Cybercriminals have also targeted Apple’s recommended browser, Safari. The most well-known Safari ransomware strain is the FBI / MoneyPak virus we mentioned above. Be careful where you click, and what you download!
Set up your defenses against Mac ransomware
The best thing you can do for your Mac and your peace of mind is to stop ransomware from infecting your computer in the first place. To start, set your Time Machine to create regularly scheduled automatic backups. For even greater safety, save your important files in iCloud as well as a peripheral device, such as an external hard drive or a USB stick. Think of it as regularly visiting the dentist — we know we should do it, but a lot of us don’t bother until we have a toothache. But you don’t want cavities or ransomware, so make sure to back up your files regularly (and maybe make this the year you finally start flossing, too).
You can power up your Mac’s defenses for free with Avast One, which identifies known ransomware variants and removes them in minutes. Plus, it safeguards your iMac or Macbook from newly developed strains and stops ransomware from encrypting your files.
So remember: back up your system and files, secure your Mac with a reliable anti-malware solution, and stay vigilant when you’re online. Mac ransomware isn’t going away anytime soon, but when you take these measures, you’re more likely to just be reading about it than dealing with it.



 Image source:
Image source:  Image Source:
Image Source:  Image Source:
Image Source: 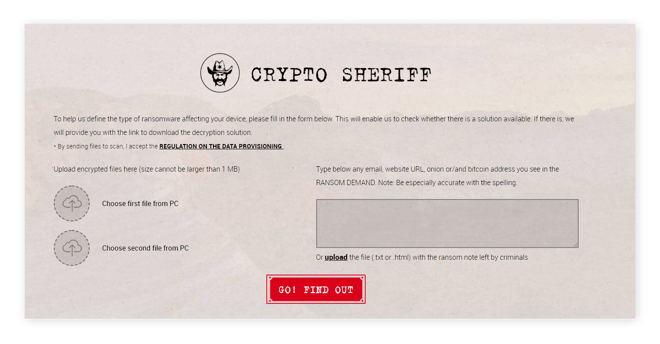
 Image Source:
Image Source:  Image Source:
Image Source: 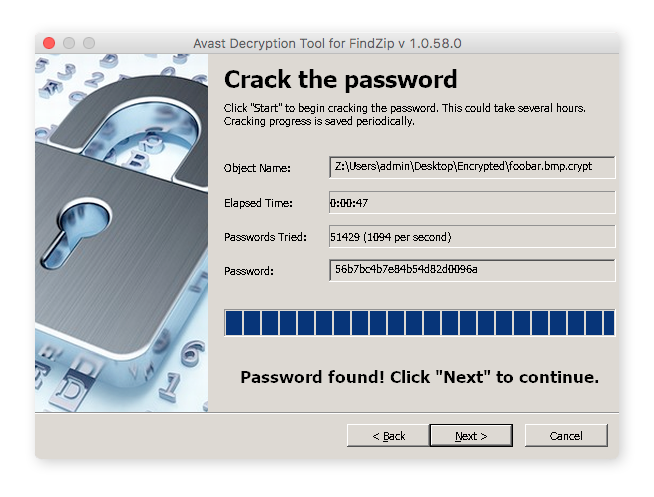
 If you get hit with ransomware, don’t pay the ransom.
If you get hit with ransomware, don’t pay the ransom.