Can you get ransomware on iPhones and iPads?
iPhones and iPads are highly resistant to malware, including ransomware. It’s very improbable that you’ll ever get actual ransomware on your mobile Apple device, because there is currently no such thing as iPhone ransomware.
Just to make that extra-clear: iPhone ransomware does not currently exist. Many people believe that iPhone ransomware is real, and cybercriminals prey on these misconceptions. Cybercriminals have successfully mimicked ransomware on Apple devices to con people into paying a “ransom”, and will probably continue to do so. Let’s dive into these “fake ransomware” techniques so you can learn to spot them and prevent becoming a victim of a ransomware attack.
If it isn't ransomware, what is it?
While there isn’t any iOS ransomware in the technical sense — as in, a type of malware that can encrypt your data or block your access to it unless you pay — there are ways that its effects can be simulated. In these cases, people fell for the scam and paid the ransom, even though their files weren’t ever encrypted to begin with.
As always, your best defense against any online threat is a dedicated cybersecurity tool, such as Avast One. Give your iPhone or iPad comprehensive protection against all the ways cybercriminals try to trick you into thinking you’ve been infected with iOS ransomware.
Fake ransomware
Some cybercriminals were able to mimic ransomware in earlier versions of iOS with the use of scareware — a malware technique that attempts to frighten victims into taking a specific course of action. Usually, cybercriminals use scareware to coerce people into buying unwanted software, especially fake antivirus software, that may even be malware itself.
But scareware isn’t just limited to software sales. A 2017 iOS scareware campaign caused victims to see an endless series of pop-up ransom notes whenever they opened Safari, Apple’s browser. Victims believed they were infected with ransomware, but in reality, it was just a coding trick that exploited a vulnerability in the way Safari handled pop-up windows.
With the release of iOS 10.3, Apple closed the vulnerability, making it impossible for the scareware to affect updated devices. Victims who hadn’t yet upgraded could remove the pop-ups by clearing their Safari browser cache. For added protection, install an iOS security app to defend against malicious websites, malware, and all kinds of other threats.
Trustjacking
Trustjacking is a still-theoretical hacking vector by which a cybercriminal abuses the Wi-Fi sync function between iPhones and desktop computers. The idea is that when someone chooses to allow their iPhone or iPad to “trust” a PC, a hacker can step in and take advantage of this wireless access to manipulate the victim’s mobile device.
Since the release of macOS Catalina, Wi-Fi sync has been available via Finder. According to the researchers who discovered this potential vulnerability, if a hacker can get victims to unwittingly “trust” their computer, they could install malware, steal data, or capture screenshots.
Always be careful when using public Wi-Fi and charging stations, and only accept Bluetooth pairings from devices you own or trust.
iCloud hijacking
If a hacker manages to guess, acquire, or crack your Apple ID password, they can lock down your device in a manner similar to what some ransomware can do. Once inside your iCloud, they’ll be able to access your Find My iPhone account, and that’s what they’ll use to lock it up. It’s the same thing you’d do if your iPhone or iPad got stolen — except with iCloud hijacking, it’s your identity that’s been stolen instead.
When you activate Find My iPhone, you can display a message on the lockscreen, and this is where the ransomware trick comes into the picture. The hacker will use this function to write a short ransom note, hoping to fool the victim into thinking they’ve been hit with ransomware.
iCloud hijacking can affect Mac computers just as easily as it can mobile devices. Be sure you’re doing everything you can to protect your Mac from ransomware, even if it’s fake ransomware. Just in case your computer ever does become infected, read up on how to remove ransomware from your Mac as well.
In previous attacks, hackers obtained victims’ passwords via phishing campaigns, which use social engineering methods to manipulate people into handing over sensitive information.
You can reset your Apple ID password even if you don’t have access to any of your devices — all you need to do is borrow someone else’s. Protect your iCloud account from password hackers with our best practices for creating strong and uncrackable passwords.
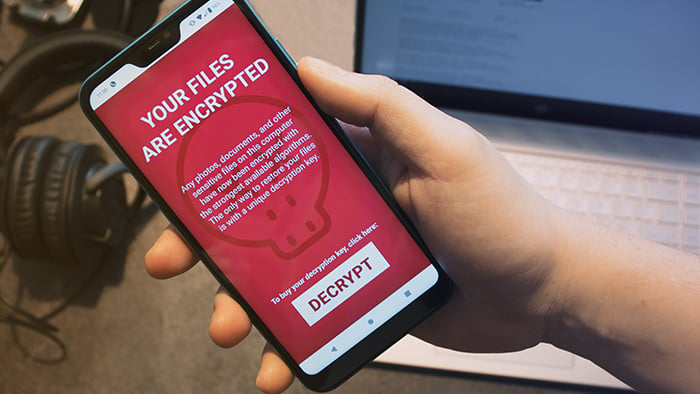
If you're positive it's iOS ransomware
You may be convinced that your iOS device is locked up with ransomware, and that’s OK. In most cases, you can remove it, though with ransomware, it’s rarely easy or simple. Filecoders — the type of ransomware most prevalent on computers — encrypt your files so that you can’t access them without a unique decryption key. This is what the hacker promises to give you after you pay the ransom.
Removing ransomware will not decrypt your files. After you remove ransomware, any data that has already been encrypted will stay that way until you decrypt it. Filecoder ransomware often removes itself to prevent researchers from studying it and decrypting its algorithms. But sometimes cybersecurity researchers are able to crack ransomware and then make the decryption keys available for free online.
An iOS ransomware infection occurring “in the wild” — that is, amongst the general public, and not in a closed research context — would be an unprecedented event. It’d take some time for mobile cybersecurity providers to develop the capabilities to counter the threat.
In any case, if you think your iPhone or iPad has somehow been hit with ransomware, here’s what you can do:
1. Immediately isolate infected devices
Any time you find malware on one of your devices, quarantine it ASAP. Disconnect infected devices from your home network, and remove anything connected to them via wired ports. Ideally, you’ll have acted in time to stop the malware from spreading to your other devices.
2. Find out which type of ransomware you have
Once more: if something or someone is threatening to hold your iPhone hostage unless you pay, it’s probably not ransomware. The scareware type of threat campaign discussed above is a much more likely culprit.
You may also find yourself the victim of doxxing. It’s not malware, but ransom does tend to be involved. Doxxing is when someone acquires sensitive personal data about you, then threatens to publish it online unless you pay a fee.
Either via your own research or with the aid of trained security experts, figure out what exactly is happening with your iPhone or iPad. It’ll make fixing the problem much easier.
3. Remove ransomware malware
Ransomware removal on iPhones and iPads isn’t so much about actual ransomware as it is about identifying and outsmarting the ransomware impersonator. For example, here’s how to get rid of fake ransomware that takes over Safari:
-
On an iPhone X or later, or on an iPad with iOS 12 or later, swipe up from the bottom and pause in the center of your screen.
-
Swipe left or right to find Safari, then close it by swiftly swiping up.
-
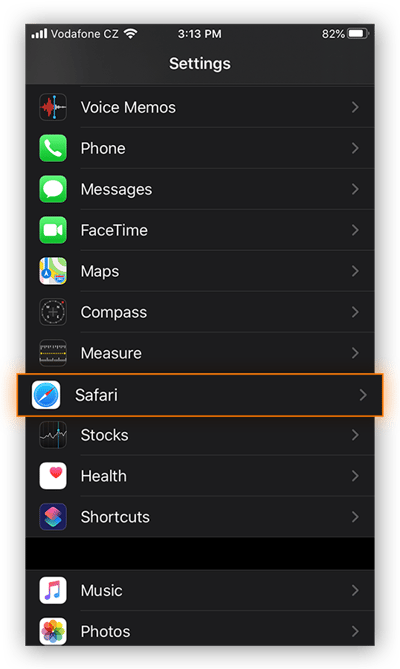
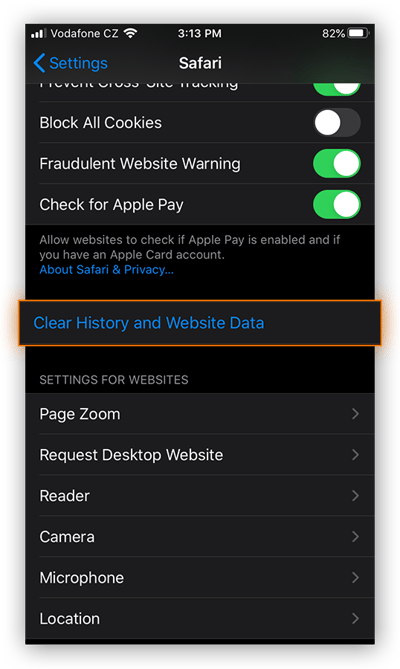
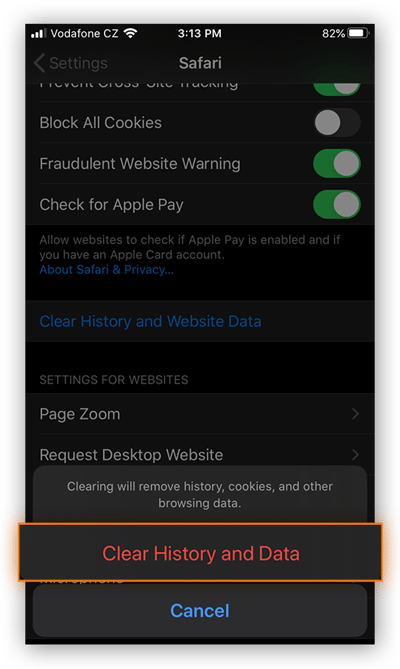
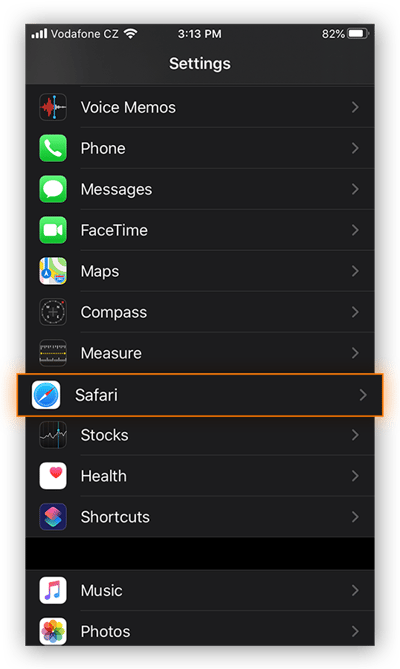
Open your Settings, then scroll down and tap Safari.
-
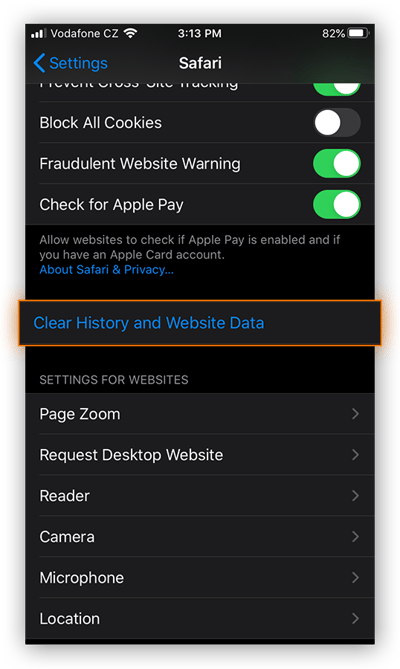
Scroll down and tap Clear History and Website Data.
-
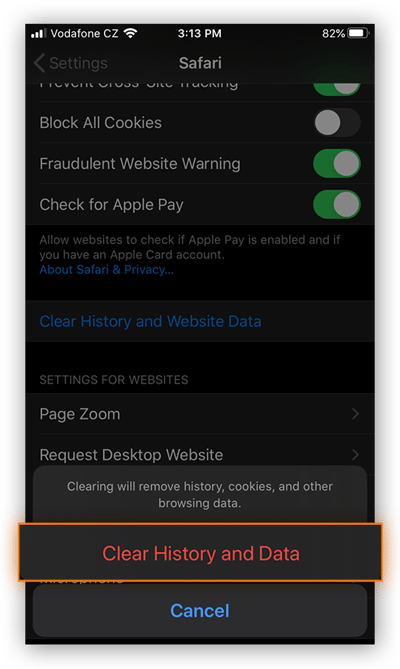
Tap Clear History and Data to confirm.
The 2017 fake Safari ransomware was ultimately a hollow threat, but it was scary enough to trick victims into paying the ransom. Keep this procedure in mind in case any similar Safari scams pop up.
If your iOS device is locked via Find My iPhone, you can circumvent the threat by resetting your Apple ID password.
It’s impossible to say what similar threats cybercriminals may develop in the future, but it’s probable that they’ll continue to be ransomware impersonators rather than actual ransomware.
(Meanwhile, if you think someone may have accessed your iPhone to spy on you, check out our spyware removal guide.)
4. Recover your encrypted files
After a traditional ransomware attack on a computer, you’ll need to somehow restore your encrypted files. The ideal method for file recovery is to restore your unencrypted files from a backup — so be sure to perform regular backups on all your devices.
There’s currently no way for any malware to similarly encrypt your files on iOS. If for some reason, you would like to recover your data, here’s how:
A. Restore from a backup
iOS automatically backs up lots of your data to iCloud. This includes your photos and videos as well as contacts, calendar, device settings, messages, apps, and more, depending on how you’ve configured your iCloud settings.
Even if the data on your device were to somehow become encrypted, your iCloud data would remain untouched, and so you’d be able to restore everything from there.
B. Don't negotiate
It’s never a good idea to negotiate with cybercriminals. Even when you’re dealing with actual ransomware, never negotiate, and never pay the ransom.
With an iOS ransom note, there’s even less of a reason to negotiate, since the threat isn’t coming from genuine ransomware. Your data isn’t encrypted, and your device isn’t actually locked, and so there’s nothing to be gained by paying or communicating with the cybercriminals.
If your iPhone or iPad is hit by a new ransomware impersonator or other hacking trick that cybercriminals create after we’ve written this article, do a quick search for the symptoms you’re seeing. It’s quite likely that someone else experienced the same thing and cybersecurity blogs are likely to cover the solution.
And while you can’t get actual ransomware on iOS, the ransomware threat is very real on Mac andPC, and Android devices. So make sure to protect your other devices against ransomware.
Defend against common iOS threats
While you aren’t going to be hit with iPhone ransomware, there are plenty of threats out there that can and do target iOS users. Unsecured wireless networks, phishing campaigns, and doxxing attacks can all compromise your sensitive personal data and leave you vulnerable to further threats.
With a built-in web shield, website safety analysis, free VPN access, and even protection against data leaks, Avast One will keep you safe against the most common iOS threats.