What is biometrics?
Biometrics is the statistical and mathematical measurement of unique physical or biological characteristics for identification purposes. In cybersecurity, the definition of biometrics refers to the use of unique biological features for digital authentication and access control.
Biometrics has a wide range of applications, especially for the future of cybersecurity and digital privacy. On the one hand, biometric technology makes signing into accounts and other security protocols quicker and easier for users, as well as much harder to hack.
On the other hand, the widespread use of biometrics raises a host of privacy and security issues due to their increased use in public surveillance. And if biometric data is exposed, the risk of identity theft and fraud rises.
What is biometric data?
Biometric data is any kind of information about an individual’s physical characteristics. DNA sequencing is the most accurate type of biometric data, followed by physiological features like retina patterns, fingerprints, and facial structure. Less accurate types of biometric data include voiceprints, hand geometry, and electrocardiograms (ECG).
To be useful, biometric data needs to be unique, permanent, and collectible, so the suitability of different types of biometric data varies depending on the application. For instance, many of us now use biometric information in the form of digital fingerprint and facial recognition technology to quickly and easily unlock our mobile phones. Such applications are seemingly impossible with a physical DNA sample.
While the biometric data definition remains constant, the kind of data — and the way it’s used — changes as technology advances. Commonly used biometric data now may eventually become obsolete as hackers learn to falsify biological identifiers. Voice bots that steal passwords are already on the rise, and retina and fingerprint bots may not be far behind.
What is biometric security?
Biometric security is the use of biometric data for identification, access control, and authentication. Hardware components such as cameras or fingerprint readers collect biometric data, which is scanned and algorithmically compared to information held in a database. If the two sets of data match, identity is authenticated and access is granted.
 Biometric security captures and analyzes biometric data to authenticate an individual’s identity.
Biometric security captures and analyzes biometric data to authenticate an individual’s identity.
Biometric security is more robust and more difficult to crack than other authentication methods such as username-password combinations, but it also leaves users more vulnerable if a data breach exposes their biometric credentials. Biometric authentication is both a powerful tool and a challenge for the cybersecurity industry.
Types of biometric security
There are different kinds of biometric security, related to the various types of biometric technology and biometric data. How a biometric login verifies your identity depends on the kind of hardware or software you’re attempting to access, and the biometric security system that’s gatekeeping it.
Biometric security is divided into three types of biometrics:
-
Biological: Biological material — such as DNA obtained from a blood, saliva, or hair sample — is highly accurate and commonly used as evidence in criminal proceedings. But biological biometric analysis is currently too slow to be used for security control in most settings.
-
Physical: Physical biometrics measure innate physiological characteristics such as the structure of the iris, face, hand, or voice. For example, iPhone biometrics lets you unlock your iPhone with your fingerprint. And when you go through a scanner at the airport, the system compares your scanned facial structure against data stored in your passport.
-
Behavioral: Behavioral biometrics records unique traits displayed in your outward behavior. Just as everyone’s handwriting varies, everyone types on a keyboard and walks just differently enough that artificial intelligence can reliably identify individuals through analyzing those traits. Browsing habits and the particular hardware used can even be put together into a unique browsing fingerprint.
Examples of biometric security
The use of biometric security is growing rapidly worldwide. In some countries, biometric security systems are mainly used to secure highly sensitive facilities and systems. In other parts of the world, biometric security and surveillance is more widespread, with biometric technology routinely embedded in public security cameras.
Here are some common examples of biometric security:
Facial recognition
A facial recognition scanner captures an image of your face and matches it against biometric information of your face that’s already been authenticated. Eye-width, bone structure, nose length, and every other detail add up to a unique facial scan for modern biometric technology.
All US passports now have chips with biometric data for facial recognition.
Fingerprint scanning
Fingerprint biometric scanners measure the unique pattern of friction ridges on the tips of your fingers. Optical scanners do this by capturing a visual image, but other types of scanners use electrical currents, ultrasound, or thermal imaging to map the ridges and valleys of your fingerprints.
Iris or retina recognition
Scanning the retina (the nerve tissue lining the back of your eyeball) is slow but extremely accurate, and it can only be done from up close. Biometric scans of the iris (the colored part around your pupil) are faster and can be done from further away, but they’re less accurate. The latest smartphones are beginning to implement retina and iris-scanning biometric security features.
Voice recognition
Voice recognition technology measures frequency, pitch, and accent, which are converted into an electrical signal and then cleaned up into distinct units of speech to help recognition software identify individuals. Apple and Android digital assistants use voice recognition to learn about your pronunciation patterns, which lets them work more quickly and accurately.
Finger and hand vein recognition
Finger and hand vein scanners use near-infrared light to capture images of blood vessel patterns near the surface of your finger or handprint. Blood flow also helps detect bogus data entries, as opposed to a fingerprint scanner that can be tricked by a copied fingerprint.
How is biometric data stored?
Biometric data storage involves three components: a sensor to collect input data, a computer to process and save it, and software to act as a go-between. The sensor records your biometric information, which is then converted into a digital format, encrypted, and sent to long-term storage.
When you provide your biometric credentials in the future, the software compares your input to what’s stored in the database to authenticate a match.
 Software compares your biometric credentials to what’s stored in a database to authenticate your identity.
Software compares your biometric credentials to what’s stored in a database to authenticate your identity.
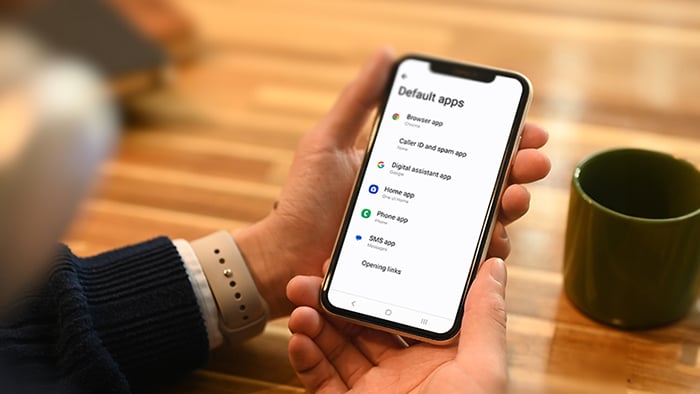
Many phones, tablets, and laptops allow biometric logins, meaning it’s now quick and easy to set up biometric security through your device’s settings. Here’s how to do it on an iPhone or iPad:
-
Go to Settings and tap either Touch ID & Passcode or Face ID & Passcode, depending on your device model and iOS.
-
Enter your passcode and then tap Set Up Face ID.
-
Follow the onscreen instructions to input your biometric data by scanning your fingerprint or face.
That’s it. Your biometric data is now stored as a digital certificate, and you can use your unique biometric identifier to access your device and encrypted apps.
Advantages of biometric security
Biometric security is becoming standard across many industries, and it’s an increasingly popular choice because it’s easy to use and offers strong levels of security.
Here are the main biometric security advantages:
-
Difficult to hack: Biometric systems are incredibly difficult to hack due to the extreme complexity and randomness of biometric data. Although biometrics can’t be guessed or cracked like passwords, they can still be compromised. Always use two-factor authentication for an added layer of security.
-
Convenient: Biometric scans are a lot faster than typing in a password, fumbling for a key, or entering a PIN. Biometric security also eliminates the need to remember multiple strong passwords — and the frustration of constantly forgetting them.
-
Always available: You can easily forget your phone, keycard, or fob at home, but it’s unlikely you'll forget your fingers or face! Biometric scanners let you log-in wherever you are, without the need for additional authentication devices.
How safe is biometric security?
Biometrics and security may seem to go hand-in-hand, but the same qualities that make biometric data so good for authentication also expose it to certain vulnerabilities and risks.
Here are some of the top biometric safety concerns:
-
Hacking: Biometrics are a lucrative target for hackers, and they attract dedicated and skilled cybercriminals. The more you scan your biometrics in different places, the more likely it is that a hacker can steal it.
-
Complacency: Biometrics on smartphones are so convenient that they can easily become second nature. This can lead to recklessness when logging in. A biometric is only as safe as the person scanning it.
-
High risk: You can change passwords, but you can’t change your biometric details. If your biometric data is stolen or lost, it could be permanently compromised.
-
Duplication: In some ways, biometric credentials are easier to obtain and duplicate than access cards or keys, because we quite literally leave our biometric footprints and fingerprints everywhere we go. Criminals are learning to copy biometric details by lifting fingerprints off glass, or even capturing voice recordings.
As governments, multinationals, small businesses, and individuals increasingly use biometric security technology, employing the right levels of OPSEC, or Operational Security, is critical for maintaining data security and preventing breaches. Learning cyber security basics for your small business can help you store your biometric data safely.
Risks to biometric security
Biometric technology is far from infallible, and there is some inherent risk. While biometrics are generally more secure than other authentication methods, the leak of biometric identifiers is potentially much more serious. And there are legitimate concerns about how governments and corporations may use your biometric data.
 Privacy
Privacy
The iPhone biometrics system records whatever you say to Siri to better understand your voice, which has led people to wonder if Alexa is always listening to whatever you say around the house. With more and more devices now holding biometric data, the risk of it falling into the wrong hands and being misused grows. And of course there are other IoT security risks.
To prevent web tracking, browser fingerprinting, and other techniques used to collect your personal data and monitor your activity, use a VPN to encrypt your traffic and an anti-tracking tool to hide your digital breadcrumbs.
 Cloning
Cloning
Your fingerprints can be lifted from physical items such as your keyboard or even recreated from a high-definition photograph. Researchers have found that facial recognition scanners can be tricked by models built from photos on Facebook and other social media sites.
Determined hackers can steal or clone biometrics. In 2015, cybercriminals stole the fingerprints of over 5.6 million US government employees, and Germany’s Chaos Computer Club spoofed the iPhone’s TouchID fingerprint reader just two days after it was released.
 Human error
Human error
The convenience of biometrics can lead to a false sense of security. Don’t show your login process to anyone, don’t leave your device unattended, and don’t dispense with other security protocols. Be extra careful with biometric credentials — once they’re compromised, they’re compromised for good.
How to ensure you remain protected
Using a biometric scanner to access your devices or apps is convenient and usually very secure. But to make sure you remain protected, multi-layered security is the best approach.
 Two-factor authentication
Two-factor authentication
Two-factor authentication (2FA) means that alongside your biometric measurements another credential is required to verify your identity. That way, if one authentication method is compromised, unauthorized access is still blocked. A popular form of 2FA are one-time security codes sent via email or SMS.
 Tokenization
Tokenization
Hiding biometric data within what’s known as a “token” reduces the risk of biometric devices being hacked. After scanning, the biometric data is converted to a randomized virtual token or code. This encrypted biometric data can only be unscrambled by someone with the right decryption key, which limits the exposure of individuals’ biometric properties.
 Ensure your software is updated
Ensure your software is updated
Like other security protocols, biometrics technology can be compromised when using outdated software, because vulnerabilities can be exploited by hackers. Updating your software is a simple and effective way to keep your sensitive data safe.
Laws and regulations
Currently, there are no federal laws in the US protecting biometric data, but some states have taken steps toward regulating the handling of biometric data and the use of biometrics technology.
Illinois requires collection of biometric data to be governed by a written policy and subject to informed consent. And New York mandates that any data breach involving biometric information must be reported to state authorities.
In the European Union, strict GDPR legislation places tight control over the collection and handling of all personal data, including biometric data. The EU has levied large fines for the improper processing of biometric data.
Keep your devices secure with Avast
With advertisers, businesses, online snoops, and hackers all after your data, controlling access to your personal information is critical. Avast AntiTrack gives you control of your online identity by blocking the collection and sharing of your browser data.
AntiTrack also uses anti-fingerprint technology to make sure your unique device identifiers aren’t visible. Browse safely, privately, and without disruptions with Avast. Try AntiTrack for free today.

 Biometric security captures and analyzes biometric data to authenticate an individual’s identity.
Biometric security captures and analyzes biometric data to authenticate an individual’s identity. Software compares your biometric credentials to what’s stored in a database to authenticate your identity.
Software compares your biometric credentials to what’s stored in a database to authenticate your identity.