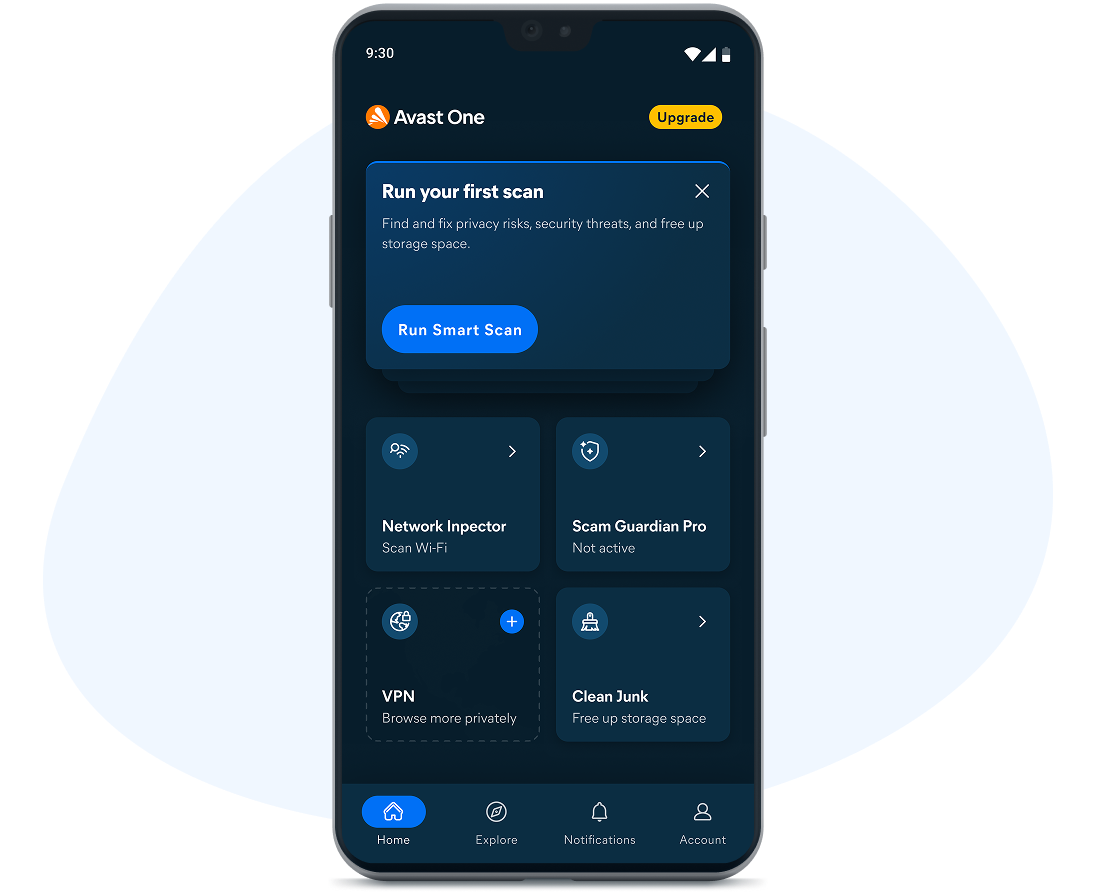
Be alerted to potentially suspicious emails before you open them. Block scam SMS messages and calls with the included mobile app. Get advanced security with our award-winning virus protection. Check possible scam messages or offers with our AI-powered Avast Assistant. Get our strongest online security in the Avast One app.

Top-Rated product 2025
Product of the Year 2026

Top-Rated product 2025

Product of the Year 2026
Get AI-powered scam protection. Feel more confident in your digital world.
Stay safer on the channels scammers target most, like SMS, phone calls, email, and websites. Get scam guidance in seconds with our Avast Assistant. Feel more confident when watching online on your Windows PC with deepfake video detection (see details).
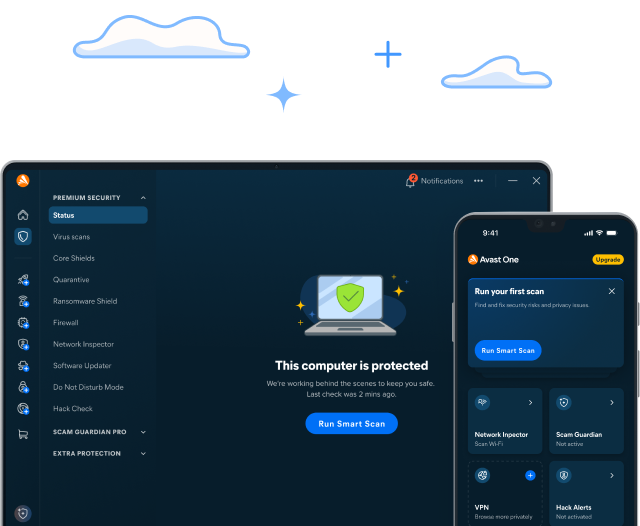
Premium Security offers award-winning antivirus, plus protection against sophisticated scams, so you can relax knowing that you're better protected.
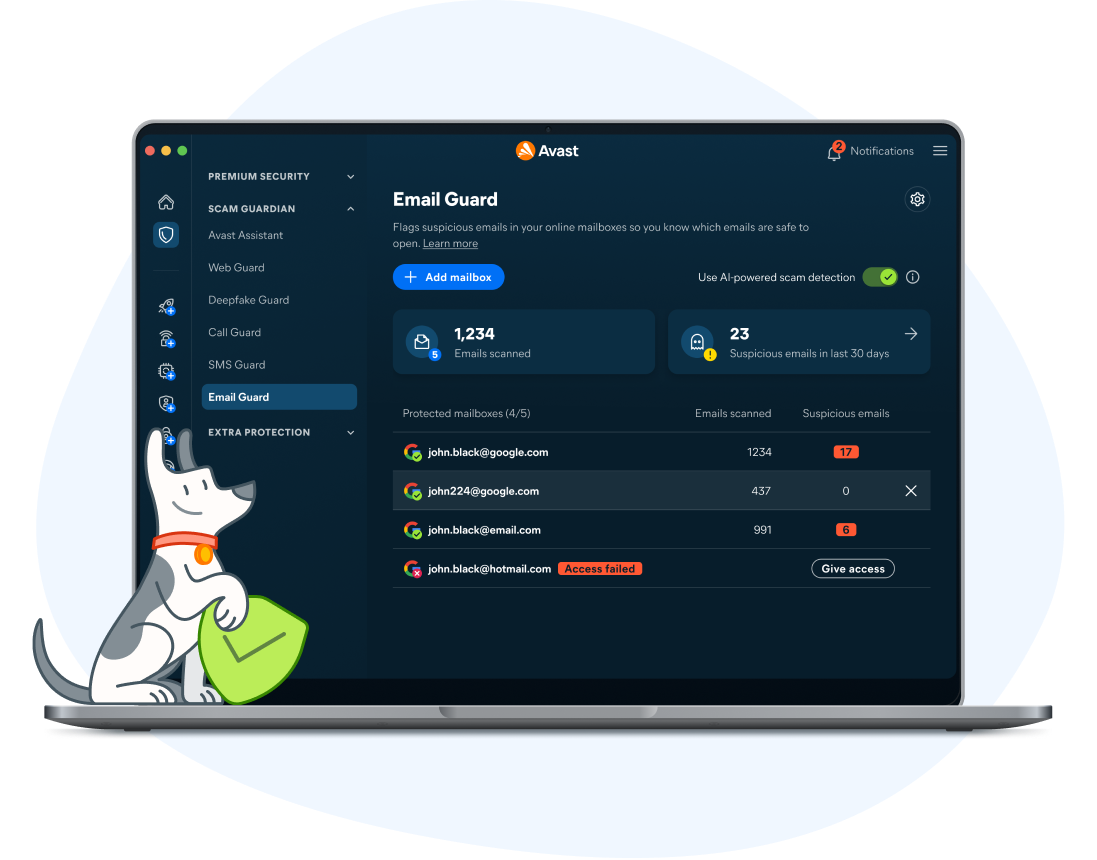
Stay ahead of potential email scams
Connect Email Guard with just a few clicks on your Premium Security. It flags potential email scams, phishing, and infected attachments before they get to you on Gmail, Outlook, and other popular email providers, no matter which computer you're using.
Block scam SMS messages and scam calls
Get advanced, AI-powered scam protection that travels with you wherever you go. It works continuously to detect sophisticated phone and SMS scams, giving you advanced protection so you'll always know when it's safe to respond. With 24/7 protection, scammers will have a hard time getting through. You can answer with peace of mind, whether it’s loved ones or a delivery update.
Shop, bank, and pay online more safely
Premium Security scans websites to make sure they're legitimate, so you can better avoid fake websites trying to steal your information. Shop, bank, and pay more securely. Worry less about your financial credentials being compromised.
Whichever devices you use, we’ve got you covered
Boost your PC’s defense against hackers trying to gain access
The last thing you need is a hacker remotely taking control of your PC and infecting it with malware or locking your files with ransomware. But no need to worry, Premium Security helps protect your PC against such attacks.

Use our Avast Assistant, powered by AI, to help detect online scams
Receive handy info about possible scam messages, offers, and more.
Block digital threats in real-time
Stop viruses, spyware, and other threats with the help of our smart shields.
Get advanced ransomware protection
Enjoy extra peace of mind because your files are safer from ransomware.
Identify and avoid fake websites
Keep yourself safer when you’re doing online shopping or banking.
Block hackers out with our advanced firewall
Stop unauthorized access to your computer with the help of our firewall.
Identify deepfake scams and fake videos
Watch more confidently as fake videos are detected for you. See details.
Keep unsafe emails away more easily
Automatically block suspicious emails with the help of advanced AI.
Prevent webcam spying
Enhance your privacy and help stop strangers from watching you.
Protect your saved passwords
Keep your browser-stored passwords better protected against theft.
Stop remote access hacking
Prevent unwanted remote access to your PC with the help of our shield.
Delete sensitive files permanently
Wipe away files so they can’t be recovered again by anybody.
Update apps to reduce security risks
Update popular PC apps automatically to help avoid security loopholes.
Open suspicious files safely
View risky files in a safe, isolated space to help protect your PC.
Avast One with Premium Security for Windows also includes
We’re award-winning by nature, not just by name
We can help protect you against advanced online threats, backed by one of the world’s largest consumer Cyber Safety networks. And we’ve been proud winners of different awards over the years. Check out some of our more recent ones below. The award-winning protection from Avast Free Antivirus and Avast Premium Security is also available in the Avast One app.

2026
“Avast Bank Mode provides isolation during financial transactions”
AVLab
Internet Banking Protection Test

2025
“95% phishing-page detection rate, no false alarms”
AV-Comparatives
Anti-Phishing Comparative Test

2025
“100% real-world threat samples detected and blocked”
AV Test
Home User Protection Test
2025
“Total Accuracy Rating: 100%, False Positives: 0%”
SE Labs
Security Evaluation Test: Home Anti-Malware

2026
"Avast Bank Mode provides isolation during financial transactions"
AVLab
Internet Banking Protection Test

2025
“95% phishing-page detection rate, no false alarms”
AV-Comparatives
Anti-Phishing Comparative Test

2025
“100% real-world threat samples detected and blocked”
AV Test
Home User Protection Test
2025
“Total Accuracy Rating: 100%, False Positives: 0%”
SE Labs
Security Evaluation Test: Home Anti-Malware
Stay Safe Virus Guarantee
Extra benefits at no extra cost
By simply keeping the automatic renewal for your Premium Security subscription active, you also keep our Stay Safe Virus Guarantee. That way, if your device becomes infected, you have access to our virus removal service, and if we’re unable to fix it, you’ll get your money back.
One solution for your online security needs
You may still be wondering...
You might be also interested in...
You're almost there...
Find and click the downloaded file {avast.exe}{avast.dmg} to complete the installation.
Initializing download....
Note: If your download did not start, click here.
Need Help? Call 855-745-3255
Important information about your subscription
What is a subscription
A subscription is the commitment from Avast to you, our customer, that we will continuously work to protect, optimise and connect you virtually in exchange for an annual fee that we bill to your bank card or PayPal account. Your subscription fee enables Avast to support you with the service you selected to subscribe to until you cancel your subscription. If your subscription has expired we can help you here.
The selected period for which you pay is measured in months and could be one month, one year or more years in length, depending on the service you selected to subscribe to from Avast. At the end of the selected period for which you have paid Avast will automatically charge your stored payment details for you to ensure ongoing, uninterrupted service.
Terms for auto-renewal and pricing
A fee for the next subscription period will be charged at the then current published price. The fees will be charged to your stored payment details up to 35 days prior to the anniversary of your subscription to Avast. These fees are subject to change. For annual subscriptions, we will notify you up to 65 days ahead of the anniversary of your subscription to remind you of the anniversary as well as the subscription fee that will be billed for the subsequent period.
Avast products are sold as continuous subscriptions, a term used to describe the uninterrupted support we give you through our software for the period of your subscription. This means that your subscription continues without interruption unless you manually cancel it before the next billing date or in case we are unable to charge your stored payment details when due. We apply this concept of continuous subscription to ensure your service never gets interrupted and you continue to benefit from our service offering.
Avast offers you many different services to which you can subscribe annually and we often discount the first year of that subscription to make it easier for you to onboard with us and enjoy our market leading services. This means that your first payment period may be discounted compared to the subsequent periods, a price difference that we make clear to you when you first selected to subscribe to our service. Prior to the anniversary of your subscription, we communicate the next payment period fee via a billing reminder.
Subscription updates, cancellations, and refunds
Avast only bills your stored payment method and has no other way of billing you for your ongoing Avast service. This means that you are responsible for agreeing to store your own payment method at first purchase and for keeping it updated to ensure that your service remains uninterrupted throughout the subscription period and relationship with us. You can cancel your subscription via the Avast Account that is linked to the email address you provided during the subscription purchase. Please visit here for more information and instructions on how to do this.
You can request a refund by contacting Avast Customer Support here within 30 days of your initial subscription or the anniversary of your subscription. For more general information regarding Subscriptions and Renewals, read here.
Customer’s responsibilities
Whilst we take our commitment to you very seriously, we also rely on you to enroll or download, install and regularly update our software. This is important as we continue to improve and expand the service you have subscribed to, and we wish you to continue to benefit from our efforts on your behalf. These ongoing improvements and expansions remain subject to the Avast EULA, which you can find here to read.