Monitor potential data breaches and get expert help with Avast BreachGuard
We can help you monitor your sensitive online information for potential data breaches and data leaks, even on the dark web. Plus, you get expert support from us whenever you need it.
Rest easy thanks to our non-stop data breach monitoring
Help protect your personal information and know what to do if your privacy comes under attack:
Monitor for data breaches 24/7
Remove personal info from data brokers
Get smart privacy advice
Get support from our team of US-based specialists
Data leaks happen every day, but BreachGuard keeps you safer around the clock
We check for leaked personal info on the dark web...
… and if your personal info is at risk...
… we give you expert advice to help resolve the issue.
Monitor your personal info and unveil potential data leaks
- Automatically scan the dark web for personal information that may have been part of a data leak or data breach.
- Stay on top of new data breaches and immediately take the right steps to help protect your personal information and avoid identity theft.
- Ensure your passwords are strong and aren’t similar to ones that have been leaked.
Reclaim your personal info from data brokers
Help stop them collecting info about you
Help prevent them from selling this information
BreachGuard helps you fix these problems
Help stop cybercriminals from exploiting your sensitive data
- Automatically send requests to remove your personal info from data broker databases.
- Make sure your info stays protected by automatically resending removal requests.
- Prevent marketers from collecting your personal info and selling it to third parties.
Strengthen your online account privacy settings
- Control the amount of private information you share publicly.
- Get tips about safer adjustments for your social media privacy settings.
- Reduce the amount of personal info companies have on you.
Get support 24/7 from our Identity Assist team
Rely on our US-based specialists to help if you fall victim to a data leak
- Get help fast when you need it
Send our team suspicious emails, websites, text messages and other communications and get a written security analysis within 24 hours. - Receive support with setting up a credit freeze
Contact our team to help you freeze your credit records with major credit bureaus. - Back yourself with credit dispute experts
We support you with handling disputes with creditors, keep you informed, and help secure your credit report with fraud alerts. - Experience real customer support
Lost your wallet? Need to inform the authorities? Need emergency funds? We help you with all that, and more.
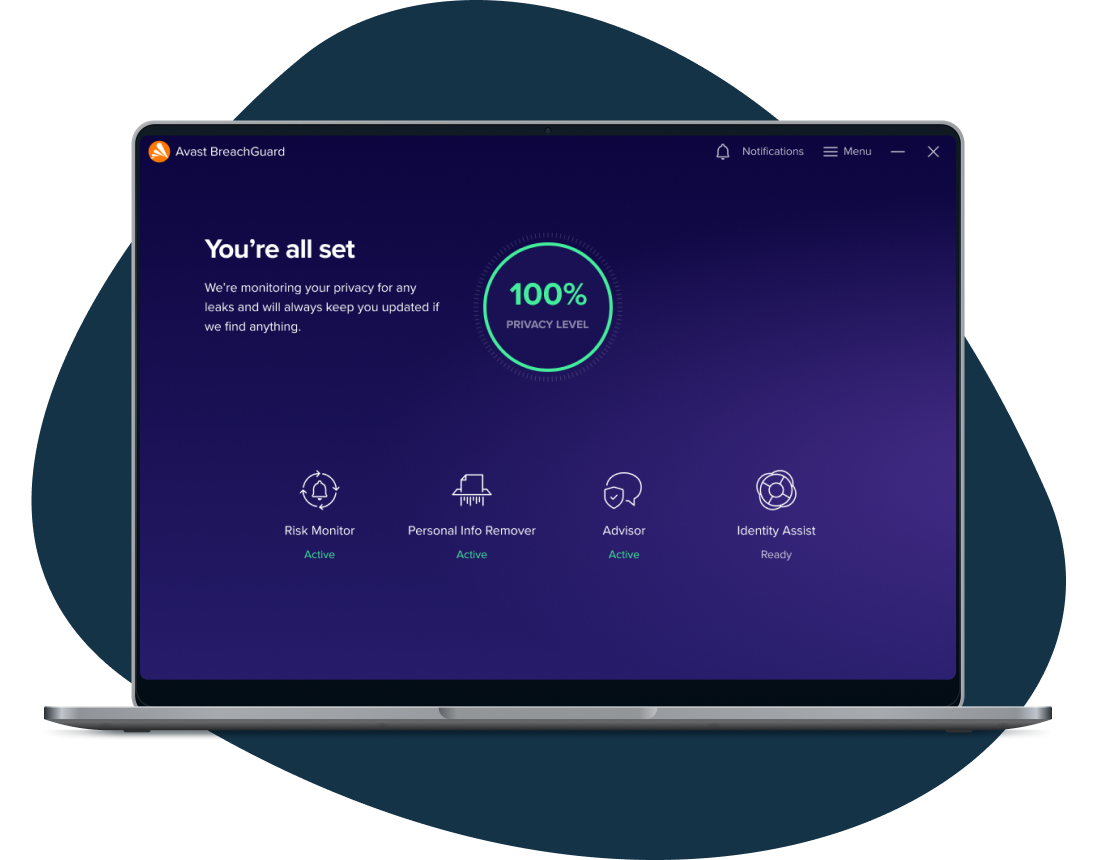
Get a clear overview of your privacy
The BreachGuard dashboard shows you your privacy score so you can easily understand your privacy level and take action to improve it.
You might be also interested in...
Important information about your subscription
What is a subscription
A subscription is the commitment from Avast to you, our customer, that we will continuously work to protect, optimise and connect you virtually in exchange for an annual fee that we bill to your bank card or PayPal account. Your subscription fee enables Avast to support you with the service you selected to subscribe to until you cancel your subscription. If your subscription has expired we can help you here.
The selected period for which you pay is measured in months and could be one month, one year or more years in length, depending on the service you selected to subscribe to from Avast. At the end of the selected period for which you have paid Avast will automatically charge your stored payment details for you to ensure ongoing, uninterrupted service.
Terms for auto-renewal and pricing
A fee for the next subscription period will be charged at the then current published price. The fees will be charged to your stored payment details up to 35 days prior to the anniversary of your subscription to Avast. These fees are subject to change. For annual subscriptions, we will notify you up to 65 days ahead of the anniversary of your subscription to remind you of the anniversary as well as the subscription fee that will be billed for the subsequent period.
Avast products are sold as continuous subscriptions, a term used to describe the uninterrupted support we give you through our software for the period of your subscription. This means that your subscription continues without interruption unless you manually cancel it before the next billing date or in case we are unable to charge your stored payment details when due. We apply this concept of continuous subscription to ensure your service never gets interrupted and you continue to benefit from our service offering.
Avast offers you many different services to which you can subscribe annually and we often discount the first year of that subscription to make it easier for you to onboard with us and enjoy our market leading services. This means that your first payment period may be discounted compared to the subsequent periods, a price difference that we make clear to you when you first selected to subscribe to our service. Prior to the anniversary of your subscription, we communicate the next payment period fee via a billing reminder.
Subscription updates, cancellations, and refunds
Avast only bills your stored payment method and has no other way of billing you for your ongoing Avast service. This means that you are responsible for agreeing to store your own payment method at first purchase and for keeping it updated to ensure that your service remains uninterrupted throughout the subscription period and relationship with us. You can cancel your subscription via the Avast Account that is linked to the email address you provided during the subscription purchase. Please visit here for more information and instructions on how to do this.
You can request a refund by contacting Avast Customer Support here within 30 days of your initial subscription or the anniversary of your subscription. For more general information regarding Subscriptions and Renewals, read here.
Customer’s responsibilities
Whilst we take our commitment to you very seriously, we also rely on you to enroll or download, install and regularly update our software. This is important as we continue to improve and expand the service you have subscribed to, and we wish you to continue to benefit from our efforts on your behalf. These ongoing improvements and expansions remain subject to the Avast EULA, which you can find here to read.